
Getty Images
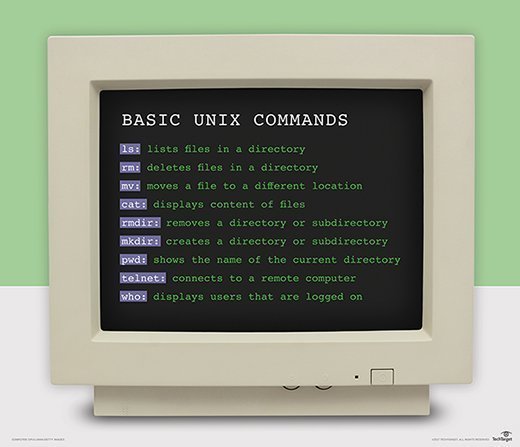
Top Unix commands: 50 must-know commands with examples
Use these 50 Unix commands to manage and modify files, navigate directories, monitor your network and users, gather data, and automate system tasks and processes.
You have thousands of commands at your disposal as a Unix administrator. However, even the most advanced administrators only use a finite number of tools and utilities on an ongoing basis. The following 50 most-used commands can provide comprehensive control over your Unix environment.
Certain differences between Unix types change administration and configuration processes on each system. Test your knowledge over commands and utilities for a better understanding of Unix.
Navigation commands
1. cd
The cd command sets the working directory of a process.
Example: Change the directory to your home directory, assuming your HOME variable is defined.
# cd $HOME
2. cp
Use the cp command to copy files.
Example: Copy the file testdb to another directory on the system.
# cp /tmp/testdb /home/frank/testdb
3. cpio
Use the cpio command to copy and move files and directories. You can also use it to back up empty directories, restore files from an archive or create an archive.
Example: Copy all files and directories in the current directory to another directory called /user/newfiles.
# find ./ -depth | cpio –pdmv /usr/newfiles
4. find
The find command searches the directory tree rooted at each given file name by evaluating the given expression from left to right, according to the rules of precedence, until the outcome is known, at which point find moves on to the next file name.
Example: Search for all files and directories in a given directory, and send them to standard output.
# find ./ -depth
5. mv
The mv command moves a file to a different directory or file system.
Example: Move the file test to the /tmp directory.
# mv test /tmp
6. rsync
The rsync command syncs data from one disk location to another.
Example: Transfer all files matching the pattern *.d from the current directory to the directory data on the machine hosta.
# rsync *.d hosta:data/
7. traceroute
The traceroute command determines a route to the host for the sake of determining network or router issues. If the domain does not work or is not available, you can traceroute an IP address.
Example: Run traceroute to an inaccessible domain to determine the cause of the problem.
# traceroute hostc.org
8. vi
The vi command brings up vi, a screen-based editor preferred by many Unix users.
Example: Open vi in editor mode to edit the /etc/hosts file.
# vi /etc/hosts
File management commands
9. awk
The awk command searches for patterns in a file and processes them. It enables a programmer to write small programs in the form of statements to make changes to text files when certain patterns appear or to efficiently extract data from those files.
Example: Count the number of lines in the file -- similar to wc –l.
# awk 'END{print NR}'
10. cat
Use the cat command to link file contents and output them for viewing or printing. You can also use it to display a file.
Example: View the /etc/hosts file.
# cat /etc/hosts
11. chmod
The chmod command changes the permission of a file.
Example: Change the permission of the file called newfile to read, write and execute (rwx) for owner, group and other.
# chmod 777 newfile
12. chown
Use the chown command to change file ownership.
Example: Change the ownership of the file called newfile to frank.
# chown frank newfile
13. exportfs
The exportfs command maintains a list of Network File System exported file systems.
Example: Export all directories.
# exportfs -a
14. ftp
The ftp command enables copying of files back and forth on different host machines.
Example: Start up ftp.
# ftp
15. head
The head command outputs the first part of a file.
Example: Display the first 10 lines in the /etc/hosts file.
# head -10 /etc/hosts
16. ls
The ls command shows information about files, such as the contents of a directory. The ls command has several subcommands, such as ls -r, which modifies the sort field to reverse the order in which files are displayed.
Example: Show a long list of file information in the data directory.
# ls –l data
17. rm
The rm command removes a file or a group of files.
Example: Prompt users to make sure they want to delete the files in the directory before doing so.
# rm –i *
18. tail
The tail command outputs the last part of a file.
Example: Display the last 10 lines of the /etc/hosts file.
# tail -10 /etc/hosts
File manipulation commands
19. alias
The alias command enables you to substitute a small or more familiar name in place of a long string.
Example: Tailor the du command to use 1K units.
# alias du=du -k
20. echo
The echo command echoes a string variable to standard output.
Example: Report back Hello World.
# echo Hello World
21. export
The export command sets the value of a variable so it is visible to all subprocesses that belong to the current shell.
Example: Export the TERM variable.
# TERM=vt220 ; export $TERM
22. grep
Use the grep command to search one or more files for a given character string or pattern. You can also use it to replace a single character or character string with another.
Example: Search for instances of hello within the file text.txt.
# grep hello text.txt
23. ln
The ln command establishes links between files.
Example: Establish a symbolic link between two files: sourcefile and newfile.
# ln -s sourcefile newfile
24. sed
Use the sed command to perform an operation or set of operations on input text and output modified text.
Example: Insert a blank line below every line that matches test.
# sed '/test/G'
Network management commands
25. ifconfig
The ifconfig command checks the network interface configuration. Use it to verify or troubleshoot a user's configuration.
Example: Show all adapter information.
# ifconfig –a
26. ifup
The ifup command starts up a network interface.
Example: Bring up the interface en0.
# ifup en0
27. ifdown
The ifdown command shuts down the network interface.
Example: Bring down all interfaces that are up.
# ifdown -a
28. netstat
The netstat command shows the network status by symbolically displaying the contents of various network-related data structures. It has a number of output formats depending on the information presented.
Example: Show information on the routing table.
# netstat –r
29. ping
The ping command sends echo requests to the host you specify on the command line and lists the round-trip time of responses. When you terminate ping, it summarizes the results, giving you an average round-trip time and percent packet loss. Use ping to determine network connection problems between two hosts.
Example: Send echo requests to hosta.
# ping hosta
Data collection commands
30. df
The df command reports file system disk space usage.
Example: Display disk space in kilobytes.
# df -k
31. du
The du command reports back the sizes of directory trees.
Example: Summarize the file size of the directory from which you run the command.
# du –s
32. env
The env command displays information about the current environment.
Example: Display all environment variables.
# env
33. id
The id command prints out real and effective unique identifiers (UIDs) and group IDs (GIDs).
Example: Show all UIDs and GIDs in /etc/passwd.
# id
34. man
The man command outputs information about commands and a keyword search mechanism for required commands.
Example: Print out information on the tar command.
# man tar
35. ps
The ps command reports back process status. It reports in two ways: the System V way and the Berkeley method. The Berkeley method does not use the dash (-) before flags.
Example: Report pack process info using the System V method.
# ps –ef
36. pwd
The pwd command displays the name of the current working directory.
Example: Report the name of the directory you are currently in.
# pwd
37. uname
The uname command prints system name and other related information about your system.
Example: Display a long list of comprehensive system information.
# uname -a
38. vmstat
The vmstat command provides a snapshot of everything going on in a given system, such as CPU usage or information on memory and I/O.
Example: Start up vmstat, and run it every two seconds for 10 iterations.
# vmstat 2 10
System automation commands
39. crontab
The crontab command manipulates cron to schedule tasks.
Example: Display your crontab file.
# crontab -l
40. enable
The enable command enables or disables a printer.
Example: Enable printer1.
# enable printer1
41. exit
The exit command enables you to exit from a program, shell or Unix network.
Example: Exit the shell.
# exit
42. gzip
The gzip command compresses files without using patented algorithms. Use gunzip to decompress a GZIP file.
Example: Compress the file file1, and rename it file2 in GZIP format.
# gzip -c file1 > file2.gz
43. shutdown
The shutdown command turns off the computer. Combine it with variables such as -h for halt or -r for reboot. Always run man before running shutdown because flags differ between varieties of Unix.
Example: Reboot the box in AIX.
# shutdown -Fr
44. tar
The tar command creates tar archives. You can use tar on previously created archives to extract files, store additional files, or update and list files. The tar command can direct its output to available devices, files or other programs. Tar can also access remote devices or files.
Example: Create a tar archive to tape device st0 -- with the contents of /home.
# tar -cvf /dev/st0 /home
User management commands
45. last
The last command shows the last users who logged in to the system.
Example: List out shutdown times and run-level changes of previous users.
# last -x
46. ssh
Use the ssh command for secure network connections and tunneling of TCP services.
Example: Connect user ken to hostb.com.
# ssh -l ken hostb.com
47. sudo
The sudo command enables you to give certain users or groups of users the ability to run commands as root or another user while logging commands and arguments.
Example: Enable users using sudo to run the adduser command as if they were root.
$ sudo -u root adduser testuser
48. w
The w command prints a summary of current system and user information. It reports current information on which users are logged in to the system and what they are doing.
Example: Print out a short list of information regarding current users.
# w –s
49. who
The who command displays information on the users who are logged in to the system.
Example: List all the available output of the who command for each user.
# who –a
50. whoami
The whoami command displays information on the user you log in as. This command can help admins who have multiple logins.
Example: Display the name of the user that you are presently logged in as.
# whoami
You can use thousands of additional commands for an even deeper control over your Unix system. Unix commands often overlap with Linux commands, so learning your way around Linux can provide deeper insight into Unix.




